We found a stable Firefox identifier linking all your private Tor identities (11 minute read)
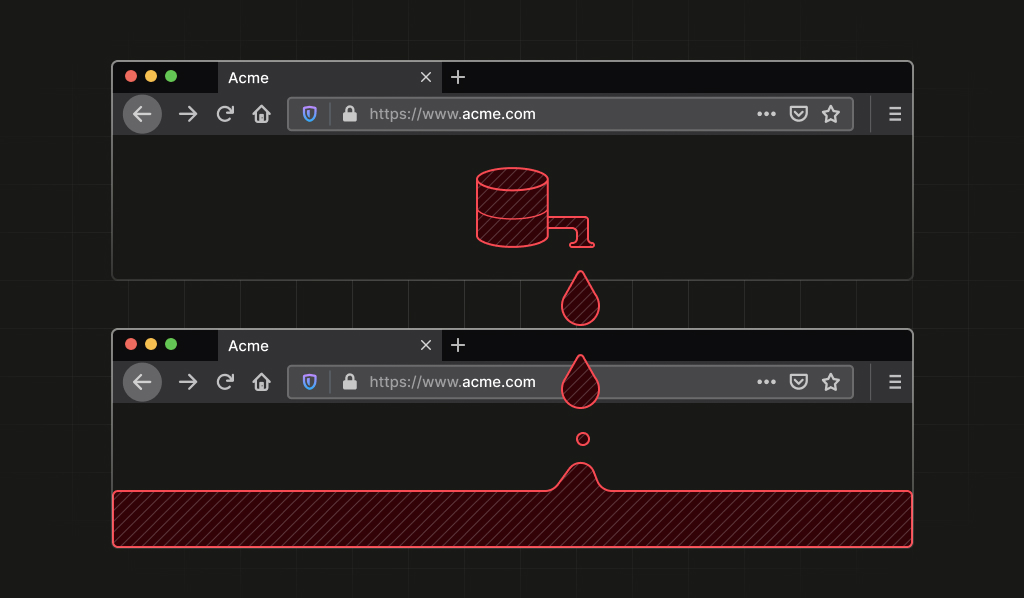
A vulnerability in all Firefox-based browsers allowed websites to track users across different origins and private browsing sessions by observing the deterministic ordering of IndexedDB database entries.
What: Researchers discovered that Firefox's IndexedDB.databases() API returns database metadata in an order determined by internal process-level hash tables rather than creation order, creating a stable identifier that persists across tabs, private windows, and even Tor Browser's "New Identity" feature until the browser process fully restarts. Mozilla has patched the issue in Firefox 150 and ESR 140.10.0 by sorting results before returning them.
Why it matters: This breaks fundamental privacy guarantees that users rely on in private browsing and Tor Browser, allowing unrelated websites to recognize they're talking to the same browser instance without cookies or shared storage. It demonstrates how seemingly harmless APIs can become powerful tracking vectors when they expose deterministic internal implementation details.
Takeaway: Update to Firefox 150 or ESR 140.10.0 to get the fix. If you're building privacy-sensitive features, audit APIs for any exposure of process-scoped state that could serve as stable identifiers across isolation boundaries.
Deep dive
- Firefox's IndexedDB.databases() API returned database metadata in an order determined by internal hash table iteration rather than creation order or lexicographic sorting
- In Private Browsing mode, database names are mapped to UUIDs via a global hash table (gStorageDatabaseNameHashtable) that persists for the entire process lifetime and is shared across all origins
- When databases() is called, Firefox gathers filenames and inserts them into an nsTHashSet without sorting, so the returned order reflects the hash set's internal bucket layout
- Because the UUID mappings are stable and hash table iteration is deterministic, the same ordering appears across all origins within a single browser process
- This creates a process-lifetime identifier with high entropy—controlling 16 database names yields roughly 44 bits of theoretical entropy (16! permutations)
- Unrelated websites can independently observe the same ordering and infer they're interacting with the same browser instance, enabling cross-origin tracking without cookies
- In Firefox Private Browsing, the identifier persists even after all private windows are closed, as long as the Firefox process keeps running
- In Tor Browser, this defeats the "New Identity" feature, which is explicitly designed to prevent activity linkability but cannot clear process-level hash table state
- The vulnerability affects all Firefox-based browsers inheriting Gecko's IndexedDB implementation, not just Firefox and Tor Browser
- The fix is straightforward: canonicalize results by sorting them lexicographically before returning, eliminating the entropy from internal storage layout
- Mozilla responded quickly and released patches in Firefox 150 and ESR 140.10.0 (tracked as Mozilla Bug 2024220)
- This demonstrates an important privacy engineering lesson: tracking vulnerabilities don't always come from direct access to identifying data, but can emerge from deterministic exposure of implementation details that leak process-scoped state across isolation boundaries
Decoder
- IndexedDB: Browser API for storing structured data client-side, used for offline support and caching
- Process-lifetime identifier: A unique fingerprint that persists for as long as the browser process runs, not just a single page load or session
- Origin-scoped vs process-scoped: Origin-scoped state is isolated per website domain; process-scoped state is shared across all tabs and windows in the same browser process
- UUID: Universally Unique Identifier, a 128-bit random string used to generate unique names
- Hash table/hash set: Data structure that stores items based on computed hash values; iteration order depends on internal bucket layout rather than insertion order
- Entropy: Measure of randomness or information content; higher entropy means more possible unique values and stronger fingerprinting
- Gecko: Firefox's browser engine, inherited by Tor Browser and other Firefox-based browsers
- New Identity: Tor Browser feature that's supposed to fully reset the session by clearing cookies, history, and using new Tor circuits
Original article
There is a vulnerability in all Firefox-based browsers that allows websites to derive a unique, deterministic, and stable process-lifetime identifier, even in contexts where users expect stronger isolation.